Do you have a backup for your router? What would happen to your home network if your router stopped working? A virtual router might be useful to you.
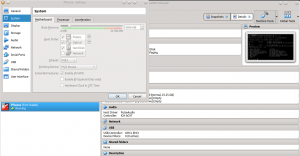
Table of Contents
My router died! Now what?
Unfortunately, my router recently failed on me. I had a custom-built pfSense router that ran strong for a couple of years and then one day it turned off and wouldn’t turn back on. I think the power supply died. My whole smart home infrastructure seemed dead. Smart speakers didn’t work because they couldn’t reach Google and Amazon’s servers. Neither my local or remote backups worked because my computers couldn’t talk to each other or the Internet. Similarly, no video surveillance, no streaming videos from my home media network or to my streaming sticks. My home security system monitoring luckily has a cellular backup, or even that would have been compromised. Everything I built no longer worked!
I didn’t want to just go out and buy another router off the shelf because I love using pfSense. Also, I didn’t want to just buy another computer and build another router (if you do, here are some good hardware options). I want to troubleshoot what is wrong with my current hardware before spending the money to buy all new hardware. Only a part or two might actually need replacing.
However, I still needed a temporary solution or nothing in the house would work! That’s when I decided to virtualize my router. I figured there was no faster solution to get our network up and running again, even if just temporarily.
Router virtualization requirements
Luckily for me, I already had everything I needed to virtualize a router:
- A stable computer you can leave on 24/7. If this computer isn’t running, neither is your router.
- At least 2 network card (NICs), preferably 3 if you will use the computer as a desktop as well. You can actually get away with one NIC, but that requires knowledge and hardware for building VLANs.
- RAM on your computer you can dedicate to the router. You only need 512MB for basic functionality.
- Some familiarity with a hypervisor. Popular ones include VMware, VirtualBox, KVM, and Hyper-V. I run
VirtualBoxon my primary desktop. EDIT: I know run Proxmox as my primary hypervisor in my home lab. - An image (.iso) of pfSense to use as the install base. You can download pfSense here.
Building the virtual router
Building pfSense inside of VirtualBox is pretty straightforward. The steps are basically:
- Create a new machine with BSD/FreeBSD type/subtype. pfSense is based on FreeBSD.
- You need to give your VM at least 512MB. If you are going to doing a lot with your router (e.g. running an IPS/IDS or VPN) you will probably want to provision more. I use 4GB as I have a lot of functionality running on my router as well as a lot of devices.
- Create a virtual hard disk (VDI). Again the size depends on what all you’ll be doing with your router. I chose 25GB for lots of growth, but I’m sure that’s overkill. My router is currently only using 1.6GB!
- Setup your network adapters. You need to bridge one adapter for your WAN, and bridge one adapter for your LAN. Remember which is which!
- Save and fire up your VM. It should ask you for a .iso file and you should point it to the pfSense image you downloaded earlier.
- Next, the pfSense installer will walk you through installation and setup. Key steps are:
- You can probably skip creating a VLAN.
- Assign a NIC to the LAN and assign your Internet connection from your modem to the WAN NIC.
At this point, pfSense should go through and install everything. Configuring your router after installation depends on your network needs. Like most routers, pfSense provides a web interface. In my case, I already had a pfSense configuration file with all my settings so I just needed to restore that to get my network back!
There are a lot of tutorials on installing and configuring pfSense, even ones specific to VirtualBox. Here are a few to get you started:
- How to install pfSense in VirtualBox – Excellent tutorial by Syed Balal Rumy on https://technicalustad.com
- Official pfSense install guide – Credit to Netgate’s official documentation
- Official pfSense configuration guide – Credit to Netgate’s official documentation
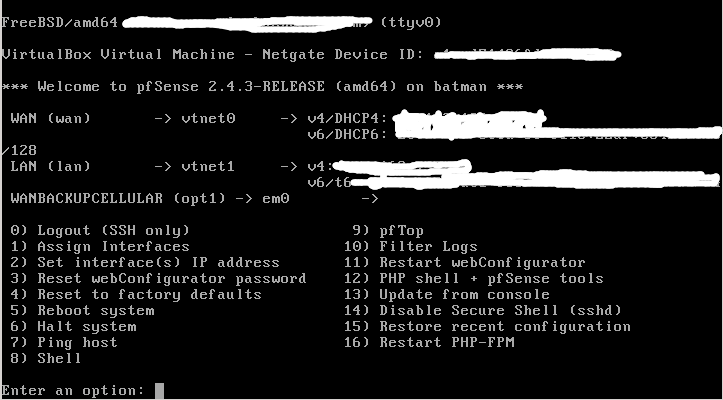
When you are all done with installation and configuration, below is the console view of what you end up with. Of course, the web interface is much nicer and easier to configure for most!
Performance and stability
Initially, the performance was a little slow. I was only getting about 25% of my usual download bandwidth. Then I discovered one of my NICs had a compatibility problem with pfSense, so I switched which NIC I was using, and then I was back to my pre-virtualization speeds. If you are buying hardware for pfSense, be sure to check on NIC compatibility, or just stick with Intel NICs. I only provided one core from my 7-year-old machine, and the web GUI was snappy and the machine was under less load than my hardware equivalent (powered by an Intel Atom).
Advantages
I have found a lot of advantages to running a virtual router:
- Snapshots, restores, and backups. I can take snapshots at any time with my VM. I get paranoid about firmware upgrades crashing or messing up my router. Virtualization takes this worry out of play because I can easily take a snapshot of the VM before any upgrades or configurations, and simply restore the working snapshot if something goes wrong.
- Easy to scale performance. If I add a lot of pfSense packages, faster and/or additional Internet connections I can easily scale up the power on my router by giving it more RAM, more CPU cores, or NICs.
- Mobility. Transferring my router to a new machine is as simple as exporting and importing to a different VirtualBox host.
Disadvantages
- Adds a layer of complexity. You have to know something about virtualization for this to work, and when things go wrong there are more layers to investigate.
- The host computer has to stay up. If your host computer fails or is turned off, there goes your router! And at times, you need to upgrade your computer.
- Changes to your host computer. It’s possible that installing new software or updates could affect your virtual router.
- Security. Some security experts think a virtual router leaves your network (especially your host) more vulnerable due to the lack of a physical layer between the router and the host. Others disagree, however. My personal take is that if I use a different, dedicated, NIC for the WAN my security isn’t much more compromised than using a separate physical router.
What’s next
I’ve been running with a stable virtual router for a few months now, and I haven’t had time to investigate what happened to my old router. I think going forward I will always at least keep a virtual router as a backup. It’s working so well, that I may just keep my primary router virtualized, and perhaps have separate hosts that can run the pfSense VM.
EDIT: After a couple of years, I have moved back to a hardware modem.
How many of you have virtual routers? Are you considering one? Let us know!
If you are interested in using pfSense, here is some additional guidance on planning an install and post-install configuration. Also, if you run pfSense, here are some tips to get the most out of it. It can be an important part of securing your home network.
If you like this content or any other content on my site please reach out and let me know on Twitter and share this with your friends, family, and social media using the sharing buttons on the right. Also, go ahead and subscribe to this site. I really appreciate it!


