If you have security cameras, smart speakers, smart bulbs, media streaming sticks or other Internet of Things (IoT) devices you should take some extra precautions to secure your network from hackers. As I mentioned in my article about fixing common wifi problems, these devices are more susceptible to being hacked because they often don’t have great security features and many are constantly accessible and/or receiving communications from the Internet. Having IoT devices on the same network as the rest of your devices without any further protections leaves you open to vulnerabilities like these and these. I have many IoT devices and I want to walk through what I do to protect my network which will hopefully inspire you with ways to protect your network.

Table of Contents
IOT devices on my network
I started thinking about security when I realized how many IoT devices I have connected to the Internet via my home network:
- Smart Speakers (Echo, Google home)
- Smart Bulbs (LIFX)
- Media Streamers (FireTV stick, Roku, Chromecast)
- Smart watches
- Connected A/V receivers
- Smart hubs
That’s a lot of devices. Even my car occasionally connects to my network to get updates. I expect to keep attaining more IOT and smart home devices as time goes on, requiring a good security solution as these devices have a higher than average potential to be hacked.
Why you want to protect your network from hacking
Protecting your network from hackers seems like an obvious desire, but what is it that we are protecting? One reason is to protect the information you have stored on computers in your home, such as:
- Personal financial information
- Photos and Videos
- Passwords
- Other personal documents
Hackers can potential make copies of these documents, hold them for ransom, or even destroy them (which is why you should keep an offsite backup of important files). Another reason is that hackers can cause havoc to your network infrastructure (reconfigure devices, brick them, etc.) causing you hours or days of lost time fixing all of these issues.
How I protect my network
I use three strategies to protect my home network from IoT devices:
- Implementing a strong firewall in my router to protect my entire network.
- Implementing firewalls on all my home computers to block accesses to services for all machines that don’t need it.
- Segregating my wifi networks by using a separate SSID and access control lists (ACLs).
Implementing a strong firewall in my router
This is paramount for protecting your home network overall. I have a home built router running pfsense, which has a robust set of security features. Some of the security features I’ve implemented are:
- pfBlockerNG. Allows me to set up block lists of known bots, spammers, malware and hacker IPs from accessing my network.
- Snort. An intrusion detection/intrusion prevention system (IDS/IPS) which proactively monitors and reacts to traffic trying to access my network.
- ClamAV antivirus protection. Blocks some known infected files from being downloaded from web pages to any device on my network.
- Proper basic firewall/router security settings such as:
- Disabling remote administration, PING, telnet, UPnP, HNAP, etc.
- Blocking almost all incoming ports except ones I explicitly set up to secure machines
My router doesn’t provide wifi to my house, but if it did I’d make sure that wifi networks are using WPA2, and have a non-default password and SSID. You can read more about good settings in my wifi improvement article.
Implementing firewalls on my home computers
I have more computers in my house than most because I repurpose old hardware into file servers, multimedia distribution systems, virtualization hosts, etc. Every single one of these machines run a firewall with rules to block other devices in my house from accessing popular network services (HTTP/HTTPS, NFS, CIFS, SSH, etc.). Now, these rules are customized for each machine. My file server obviously allows most computers to access its files and my web servers allow HTTP/HTTPS connections. By default, however, my firewall rules are set up to block all my IoT devices from accessing anything, unless I write in an exception. All of my computers run Linux, and I use the UFW firewall software to accomplish this.
Segregating and securing my IOT wifi network
I may have buried the lead with discussing this security step last as I believe this is the key to protecting your network, especially if somehow your IOT devices are hacked. I took the following steps with my TP-Link EAP225 and EAP245 access points (see my review of these excellent APs here):
- Created a separate SSID for my IoT devices.
- Used static DHCP in my router to assign computers into IP ranges (IoT devices are in their own range).
- Setup an ACL for my APs that stop devices from connecting to non-IoT devices.
- Applied that ACL to the SSID I set up in step one.
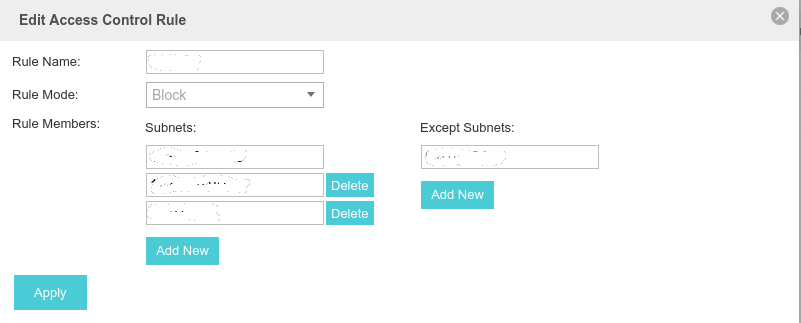
Now, when I get a new IoT device, I connect it to the IoT specific SSID. This blocks them from accessing other devices I specified in the ACL.
Simpler ways to protect your network from IoT
This may seem really complicated for some. There are simpler ways to protect your network. Now you can buy wifi routers and access points that have IOT protections built in, such as the Norton Core, Cujo, and Bitdefender BOX. These devices are a bit pricey and often require you to pay for subscriptions. You can check out my Buyer’s Guide for other router and access point options.
You can connect your IoT devices to a segregated guest network. However, if devices require access to a device on your non-guest network, you may be out of luck. For example, chromecasting, or streaming video to a media stick from your NAS.
Final Thoughts
I hope you found this article helpful. You also might want to check out additional tips for keeping your home network secure. Once you’ve got your network secure, here are 5 ways to protect yourself from data breaches. Every bit of cybersecurity helps!
Editor’s note: This page contains some affiliate links. For more information read our disclosures.


